Featured on Home Page
Smarter City Security: Mapping the Path to Success
Through partnerships, grant competitions and technology, cities nationwide are utilizing security to push their economies and quality of life forward.
August 1, 2016
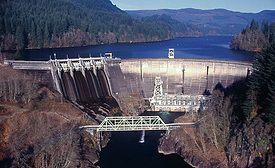
Critical Infrastructure Sector Battles Growing Variety of Security Threats
Enterprise security executives at utilities are geared up for everything from terrorism to copper theft.
August 1, 2016
Retrofit Fits the Bill for Outdated Security Technology
Even under extremely difficult lighting conditions, day/night cameras achieve optimal image results, making them a popular choice for surveillance.
August 1, 2016
Video Surveillance Analytics is a Deal for Retailers
Loss prevention and merchandizing are coming together, as retailers see value in data mining images collected by security video.
August 1, 2016
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2024. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing