Leadership & Management
Who is Facilitating Insider Threats?
Are enterprises in an impossible situation when it comes to dealing with insider threats?
September 1, 2014
Extending Dignity and Respect to Security Officer Contracts
Virtually every company will have a statement of some kind extolling the senior leadership’s commitment to treating people with dignity and respect.
August 1, 2014
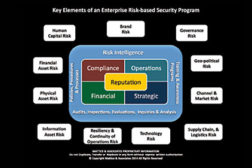
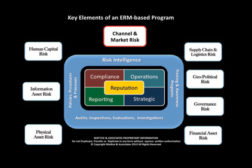
Managing Risk Across the Enterprise
The key to the risk-based security program is that no matter what issue you examine, every one of them affects the reputation of the enterprise in one manner or another.
July 1, 2014
Controlling Brand Risk
How the market perceives a company and its brand(s) ultimately dictates success or failure.
June 1, 2014
How to Keep Up with Emerging Technologies and Risks
consumers hundreds of billions of dollars annually. In the United States, credit card fraud resulting from cyber intrusions has skyrocketed.
April 1, 2014
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2024. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing