Home » threat intelligence
Articles Tagged with ''threat intelligence''
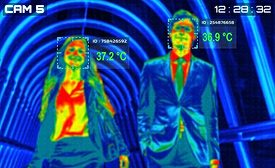
Thermal Cameras to Fight Coronavirus in the Workplace?
What are some practical tips for using thermal cameras to detect COVID-19?
August 12, 2020
How CISOs Can Effectively Measure and Report Security Operations Maturity
It's not the number of moving pieces in your security program that matter; it's how those pieces are making your organization more resilient that truly counts. How do you achieve that goal?
August 10, 2020
The Rise of Extremism
The rapid growth of extremist groups provides many challenges for enterprise security.
June 8, 2020
Cyber Tactics
Better Mobile Security with a Mobile Threat Defense Plan
What is a Mobile Threat Defense (MTD) and do you have one?
March 1, 2020
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2024. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing