Printer security: Simplicity is the key to success
Earlier this year, an investigation team hijacked thousands of printers all over the world to show just how vulnerable these devices can be if left unprotected. Too many organizations and individuals do not properly address them when discussing security strategies, physical or cyber, but if left unsecured, these devices can be real vulnerabilities. In particular, with the ongoing decentralization of workforces everywhere due to the “new normal” brought on by pandemic-related social distancing requirements, the attack surfaces print devices pose have only increased.
However, the key to any successful security measure may be simplicity, and fortunately, with a few straightforward, proactive measures, enterprises and employees can safeguard sensitive data. Risks must be addressed at three different levels: the user, the device, and the network.
User Level
The first way to protect printing devices is to educate the user since most attacks are initiated by an employee unknowingly allowing an attacker to gain access. Whether this education takes the form of email alerts from the IT department, training during the onboarding process, or through regular teaching sessions, informing employees of the best practices for device security can go a long way towards improving the security posture around printers.
Device Level
Information can easily be stolen from the device itself, as anyone with access can remove printed documents from the tray if the proper precautions are not taken to control accessibility. Relatedly, data stored on a hard drive in a printer can be a treasure trove if not properly protected or erased when the printer is decommissioned. For these reasons, ensuring the physical security of printers is an important step towards overall device security.
The easiest action users can take to uplevel their device security immediately is change the default or admin password. When updating the password, be sure to adhere to best practices, such as using eight characters or more that are a mix of both uppercase and lowercase letters, special characters, and numbers. In addition, avoid using common dictionary words and personal information in your device’s new password. Making this simple change is the first step to adding barriers for bad actors looking to gain access to the device. Again, just because it’s a simple step doesn’t mean it’s not important.
Users should also keep up with the latest firmware updates. These updates are shared by manufacturers for a reason, and being remiss in keeping devices up-to-date can open them up to attackers. Some updates are specifically meant to patch known security vulnerabilities, so you want to give your device a fighting chance by giving it the most up-to-date firmware protection.
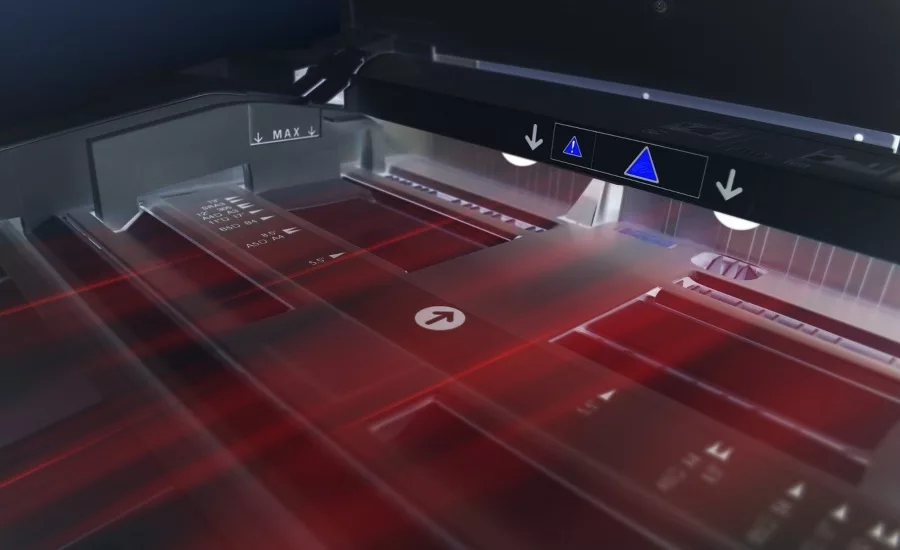
IT staff should also set up pull printing in the office. Pull printing protects your data by limiting access to the files being printed. For example, pull printing will only allow a person to retrieve a document from the device once they’ve authenticated themselves, which can be done in the form of inputting a PIN or utilizing NFC ID card readers. These methods of authentication ensure that only the person authorized to print those documents is able to do so, minimizing the possibility of data loss at the device. Pull printing utilizing ID cards has the additional advantage of lowering risk for employees in today’s COVID world by minimizing contact.
Network Level
On the network side, printers can be the point of least resistance to enterprise-wide access. Once the network-connected device is compromised, bad actors can work their way through the corporate network, laddering up to ever-more sensitive data as they go.
One solution that organizations can employ to protect data at the network level is IP filters. IP filters ensure that those outside pre-approved IP addresses are unable to access the device. This helps protect not only the data on the devices, but also the network as a whole.
Having security policies in place around print devices can also help uplevel security. For example, organizations should implement a policy around disabling unnecessary ports and protocols, which minimizes the number of access points bad actors can use to gain entry to device data and functionality by closing an easy to exploit gap in security.
Another important policy to consider is device permissions. Organizations should ensure that changes to device settings can only be made after inputting the admin password. Restricting access to device settings to only those that know the (newly strengthened) admin password can protect against insider threats and bad actors wishing to change settings.
Smart, automated document management systems can also add an extra layer of protection by, for example, verifying identity so that the person authorized to print or scan the document is the one actually doing so. In addition to authenticating users for jobs, these systems can also manage what features of the device each user is allowed to utilize based on that authentication. This way, organizations can ensure that each user is permitted to perform an action, minimizing the risk of access by unauthorized users to certain features.
Newer document management software can also systematically redact personally identifiable information, which reduces the damage if a document does, in fact, fall into the wrong hands. Personally identifiable information that is stolen can be utilized later in phishing attacks, acting as yet another way that hackers can access the network and steal information or cause damage, so minimizing the risks of this type of data being compromised is paramount.
Ultimately, although printers can be a security weak spot if left unprotected, there are a few easy steps that can be taken on the user, device, and network levels to drastically uplevel the protection of data passing through printers as well as the protection of the network as a whole. Be it at home or in the office, when it comes to security, simplicity can always be the key to success.
This article originally ran in Security, a twice-monthly security-focused eNewsletter for security end users, brought to you by Security Magazine. Subscribe here.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







