Document Security Leads to Enterprise Security
Society’s access to - and reliance on - information is historically unprecedented.
Our ability to create, share, and manage gigabytes of information has accelerated the development of modern world. There is not a single industry that is unaffected or that has not benefited from the wealth of data readily available to us every day, all day.
The need to protect this data and information is also unprecedented. The wrong information in the wrong hands can have disastrous results at the national, corporate, and personal levels. In fact, in the coming years, North American businesses are expected to spend more than $101 billion on cybersecurity, according to a Fortune report.
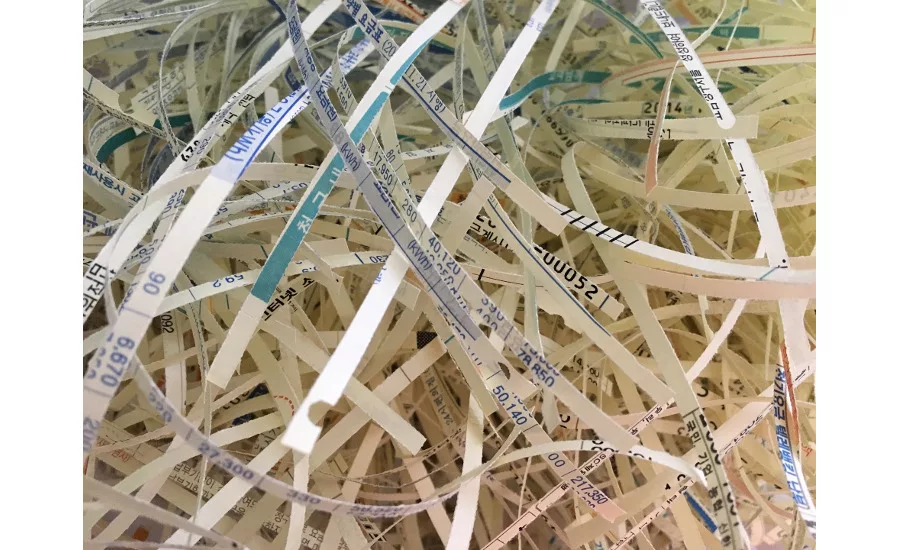
Despite all of the attention and the amount of money and time that is spent on cybersecurity, it is important to consider and protect the amount of information and data that is non-digital. There are many businesses that rely on paper documents and paper files that contain data such as medical records, salary details, credit card information, social security numbers, personal addresses and more.
In fact, according to the Identity Theft Assessment and Prediction report by the University of Texas, more than 53% of identity theft breaches are non-digital. Even more, the probability of having a material breach in the next 24 months is 27.9%, Cost of a Data Breach study by the Ponemon Institute.
Yet, North American businesses spend less than $4 billion towards document security, which includes document management and secure destruction.
Cyber and data security without an integrated document security and shredding program is not protecting all your information; your organization is still at risk and, possibly, not compliant with privacy legislation.
Keeping confidential information secure is essential. Holding on to documents you no longer need that are not kept in a secure area can pose a threat to your identity and can cause a data breach that can put you and/or your organization at risk as well as tarnish your reputation.
Here are 5 reasons why you should implement a formal document destruction program.
- To safeguard your organization’s data and reputation from theft and breaches.
- To ensure compliance with federal, state and industry regulations and avoid penalties, fines or legal action.
- To save money. Manually ripping or cutting documents can take a long time and can incur large costs in terms of labor. Even more, you can save on storage space, as paper can take up a lot of space in storage areas, in filing cabinets or other parts of the office.
- Recycling is not an option. Just because you recycle your data doesn’t mean it is secure. Recycled paper can be given away or sold. From a risk management perspective, recycling your sensitive paper documents is risky and not in your best interest.
- Consumer Trust. A breach of client confidentiality can lead to lost business and trust issues that can be impossible to overcome. Shredding documents as soon as you are done with them can decrease the risk of data and sensitive information from falling into the wrong hands.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







