Home » cybersecurity tools
Articles Tagged with ''cybersecurity tools''
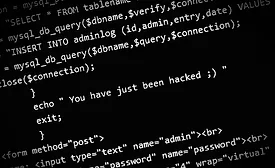
How to Change Behavior for Stronger Security System Cybersecurity
How Healthy Are Your Cybersecurity Habits?
June 27, 2017
Preparing for Inevitable Cyberattacks on Physical Security Systems
Tips on Pre- and Post-Installation Readiness
June 13, 2017
RSA 2017: The "Culture" of Cybersecurity Collaboration
Platform integration, centralized management and a holistic view of risk were recurring themes at RSA this year.
April 1, 2017
Integrates Tested Tools for Network Monitoring and Security
IntellaStore II from APCON
December 1, 2016
Simulates Attacks on Networks to Test Responses, Security Levels
Red Team from NTT Security
December 1, 2016
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing